Right now, 70% of enterprise IT budgets are consumed entirely by maintaining technical debt [31]. If you are a CTO or VP of Engineering, you already know this math. You have likely spent the last five years requesting capital expenditure to strangle a monolithic core, only to be told by the finance department that backend modernization does not deliver immediate customer value. However, the regulatory landscape of 2025 to 2027 has fundamentally altered this calculus. With a dense cluster of new mandates like the Digital Operational Resilience Act (DORA), the Network and Information Security Directive 2 (NIS2), and the EU AI Act taking effect, compliance is no longer a periodic legal checklist. It has become a real-time engineering constraint.
Technology leaders are increasingly weaponizing these immovable regulatory deadlines to bypass corporate inertia. They are using compliance as a strategic Trojan Horse to fund the deep architectural modernization that their systems have desperately needed for a decade. This is not a vendor pitch about effortless digital transformation. This is a battle-tested playbook on how to leverage the threat of multi-million dollar regulatory fines to fund data decoupling, API abstraction layers, and modern event-driven architectures.
The 2025-2027 Regulatory Pressure Cooker: A New Engineering Constraint
The period between 2025 and 2027 brings an unprecedented density of concurrent legislative mandates. The European Union is functioning as the global regulatory vanguard, and these directives force sovereign and multinational enterprise IT architectures to adapt rapidly. Compliance has shifted from a post-hoc auditing exercise handled by legal teams into a continuous pipeline requirement managed by platform engineering.
DORA & NIS2: The End of Manual Audits
DORA, which became mandatory for compliance in January 2025 [1], fundamentally shifts the regulatory focus for financial entities. Historically, financial regulators focused on capital liquidity. Now, the focus is squarely on Information and Communication Technology (ICT) resilience [2]. DORA mandates that organizations maintain highly accurate, real-time registers of all ICT contracts and deploy strict incident reporting frameworks.
Parallel to this, the NIS2 Directive expands its scope from earlier iterations to cover 18 highly critical sectors [5]. NIS2 establishes personal executive accountability for cyber risk management. Most critically for engineering teams, it mandates a rigorous three-phase incident reporting structure: a 24-hour early warning, a 72-hour incident update, and a one-month final report [11].
These directives jointly mandate a pivot from manual security auditing to real-time autonomous telemetry. Legacy Security Operations Centers (SOCs) that rely on batch-processed log aggregation are structurally unable to achieve the sub-one-hour Mean Time to Detect (MTTD) necessary to satisfy these mandates. When an auditor asks for a complete blast radius report within 24 hours of an anomaly, a system that takes 48 hours to run a database query is mathematically non-compliant.
EU AI Act: Immutable MLOps and Data Governance
The EU Artificial Intelligence Act introduces phased, risk-based constraints on algorithms. With unacceptable risk AI models banned in early 2025, and rules for General-Purpose AI (GPAI) taking effect by August 2025 [13], engineering teams are forced to rethink how they build and deploy models.
You can no longer deploy a machine learning model via an ad-hoc script and hope for the best. The AI Act requires engineering teams to build continuous lifecycle MLOps pipelines integrated with immutable compliance logging. High-risk systems require extensive, version-controlled documentation on training datasets, validation methods, and systemic limits [17]. This permanently alters how data lakes and algorithmic deployments are governed. It forces the adoption of strict data lineage tools and pipeline-as-code methodologies. If you cannot mathematically prove exactly which dataset trained the model making a specific decision in production, you are operating outside of compliance.
PSD3 & eIDAS 2.0: Forcing Cryptographic Agility
For the financial and identity sectors, the convergence of the Payment Services Directive 3 (PSD3) and eIDAS 2.0 acts as a massive technological forcing function. PSD3 mandates stronger anti-fraud mechanisms and deeper Open Banking integrations [22]. It effectively kills highly vulnerable PSD2 authentication methods, such as SMS OTPs, replacing them with converged, behavioral-based Strong Customer Authentication (SCA).
Simultaneously, the mandatory rollout of the European Digital Identity Wallet (EUDI) by 2026 under eIDAS 2.0 requires systems to rely on advanced cryptographic agility [24]. Organizations must shed static legacy key management practices. To support dynamic step-up authentication and high-assurance identity binding, engineering teams must implement automated certificate lifecycles. While this requires a heavy architectural lift, it carries massive operational benefits. Industry data suggests that leveraging eIDAS 2.0 capabilities is projected to reduce long-term KYC operational costs by up to 40% [24].
These mandates collectively dictate that compliance is now an architectural problem. If your infrastructure cannot support mutual TLS, dynamic identity provisioning, and continuous automated telemetry, you cannot simply buy a vendor compliance tool to bolt onto the side. You have to rebuild the foundation.
Structural Failure: Why Legacy Systems Cannot Be Patched into Compliance
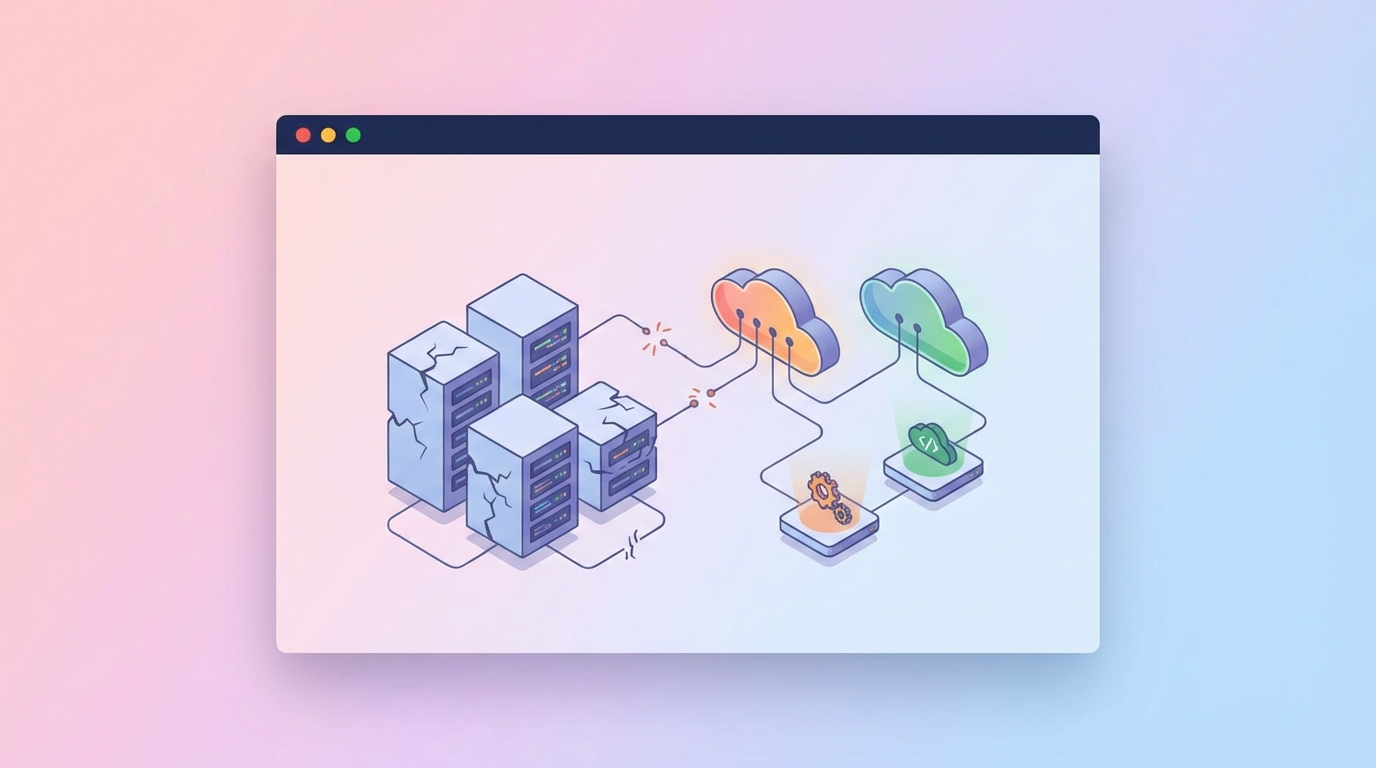
The primary barrier to surviving the 2025-2027 regulatory cluster is accumulated technical debt. Legacy infrastructures, typically defined by monolithic application architectures, batch processing, and siloed relational databases, are physically incapable of hitting the SLAs demanded by new compliance directives. Attempting to patch these systems into compliance is an exercise in futility that drains engineering resources and drastically increases operational risk.
Monolithic Silos vs. Real-Time Telemetry
Modern compliance frameworks demand agility, precise data governance, and proactive security monitoring. Legacy systems contradict these principles by design. Because they were engineered with monolithic architectures, these systems often operate on a one-size-fits-all output model. When processing a transaction, they might generate reports or data feeds that expose excessive Personally Identifiable Information (PII), directly violating the data minimization principles of GDPR and similar frameworks [2].
Furthermore, legacy data is chronically siloed. In the financial sector, communications, phone logs, and transaction records often reside on entirely separate, disconnected mainframes or localized servers. When regulators under DORA or NIS2 demand a complete conversation trail within a 24-hour window, compliance teams are forced into manual, error-prone data retrieval processes.
The limitations become glaringly obvious in transaction monitoring. Legacy Anti-Money Laundering (AML) systems utilizing outdated rule-based logic simply choke on modern trading volumes. Because they lack dynamic, machine-learning-driven scoring capabilities, these legacy systems generate false-positive rates as high as 95% to 98% [13]. This creates severe operational bottlenecks. Analysts spend their entire day clearing false alerts while genuine anomalies slip through undetected. The system is functioning exactly as it was programmed decades ago, but the regulatory environment has moved on.
IAM Deficiencies and the Zero-Trust Mandate
Identity and Access Management (IAM) is where legacy systems fail most spectacularly under modern audits. Frameworks like NIS2 and PSD3 explicitly demand Zero Trust architectures and granular, attribute-based access controls. Older platforms frequently rely on hardcoded credentials or single-password logins. They completely lack native support for Multi-Factor Authentication (MFA) and do not expose the modern Application Programming Interfaces (APIs) necessary to integrate with centralized identity providers like Okta or Entra ID [1].
This is not just an operational headache. It is a critical security vulnerability. According to the 2024 Data Breach Investigations Report by Verizon, over 60% of data breaches involve legacy systems with inadequate security controls [5, 33]. These aging applications run on unsupported operating systems that cannot receive modern security patches. They contain outdated software libraries filled with known Common Vulnerabilities and Exposures (CVEs). You cannot enforce the principle of "never trust, always verify" on a 1990s-era monolithic database that assumes any request originating from the internal network is safe.
The 42% Premium of Keeping the Lights On
The financial burden of keeping these outdated systems functional is staggering. Industry data suggests that 70% of enterprise IT budgets are consumed strictly by maintaining technical debt [31]. But the cost goes deeper than just standard maintenance.
According to IDC models, operating on legacy architecture carries an estimated 42% overhead premium compared to modernized cloud equivalents. This premium is driven by multiple factors. First, there is severe talent scarcity. Engineers who know COBOL or proprietary legacy mainframe languages are retiring, driving up contracting costs. Second, there are highly inflated extended support licensing fees charged by vendors for maintaining end-of-life software.
You are paying a massive premium just to keep the lights on, and the system is still failing regulatory audits. Every dollar spent on patching a legacy monolith to appease a compliance requirement is a dollar incinerated. It adds zero business value, introduces complex operational workarounds, and merely delays the inevitable system collapse.
Source: Industry Data & IDC Models (2024)
Regulatory bodies are no longer accepting promises of future improvement. They are tracing compliance failures directly to these hard technological limitations and issuing fines that dwarf the cost of a proper modernization project.
The Financial Catalyst: Weaponizing Deadlines for CapEx

Because maintaining technical debt drains the baseline operational budget, securing net-new capital for digital transformation is notoriously difficult. Business stakeholders want to fund features that drive revenue, not backend plumbing refactors. However, the existential threat of regulatory penalties, combined with strict deadlines, fundamentally changes the conversation. Compliance acts as a Trojan Horse, unlocking previously denied capital expenditure to address foundational technical debt.
Bypassing Corporate Inertia with Immovable Mandates
Corporate inertia is the default state of enterprise IT. If a system is processing payments, the business instinct is to leave it alone, regardless of how fragile the underlying code has become. But when the European Union states that failing to comply with NIS2 will result in executive liability and fines up to 2% of global turnover, the inertia breaks.
CTOs are using these mandates to reframe the modernization discussion. The conversation shifts from "we need to refactor the database to reduce latency" to "if we do not decouple this data layer by October 2025, we will be legally barred from processing transactions in Europe." By mapping specific legacy technical gaps to explicit regulatory violations, engineering leaders turn backend modernization into a non-negotiable risk mitigation strategy. Capgemini estimates that 70% of large enterprises explicitly prioritize modernization projects driven by compliance. The deadline becomes the ultimate forcing function.
Following the Money: Surges in IT and Cyber Budgets
Driven by this pressure cooker of mandates, global IT and cybersecurity budgets are surging. Enterprises recognize that they cannot patch their way out of this cluster. They have to build.
Gartner forecasts that 2025 IT spending will reach between $5.43 trillion and $5.61 trillion, fueled directly by sweeping compliance and GenAI mandates [31]. While analysts diverge slightly on the exact magnitude, forecasting between 7.9% and 9.8% year-over-year growth for 2025, the trajectory is undeniable. By 2026, growth is projected to exceed 10.8% [31].
Cybersecurity is the fastest-growing sub-segment. Global cybersecurity spending is projected to reach $240 billion by 2026, representing a 12.5% increase [31]. According to PwC, 77% of companies are increasing their cyber budgets directly in response to these mandates. This influx of capital is not just buying higher-tier firewall licenses. It is funding the replacement of legacy perimeters with AI-driven, compliance-ready telemetry systems and modern identity fabrics. The money is flowing, and smart engineering leaders are directing it toward structural debt retirement.
The True Cost of Regulatory Fines
If the board hesitates to approve the CapEx request, the alternative is catastrophic executive liability and massive fines. Regulatory bodies have lost patience with large enterprises pleading legacy complexity. They are levying massive penalties that explicitly cite outdated infrastructure as the root cause.
In 2020, Citigroup was hit with a $400 million fine by the OCC and the Federal Reserve Board for enterprise-wide deficiencies in risk management [8]. The root cause was architectural. Citigroup's infrastructure was a fragmented, 1990s-era tech stack accumulated through unchecked M&A activity. These discrete systems could not interoperate to provide the required enterprise-wide risk reporting. Despite promises to modernize, the institution received an additional $135.6 million fine in 2024 for insufficient progress [10].
The aviation sector offers an equally brutal lesson. Southwest Airlines was hit with a $140 million penalty as part of a broader $800 million crisis cost directly linked to consumer protection compliance failures [Stream 2]. The underlying cause was a 1971-era scheduling system that structurally collapsed under weather-related load, leaving the airline entirely blind to crew locations.
In the financial sector, Deutsche Bank was fined $124 million in 2022 due to poor AML controls linked to outdated technologies that slowed investigations [15]. When an enterprise loses nearly a hundred million dollars annually due to legacy system failures, the $10 million CapEx request to strangle the monolith becomes a highly rational financial decision.
Source: Regulatory Enforcement Reports
These fines demonstrate that technology constraints are no longer just an IT problem. They are a board-level existential risk. Weaponizing this reality is the most effective way a CTO can secure funding.
The Trojan Horse Playbook: A Phased Architecture for Modernization

Securing the funding is only the first hurdle. Executing the modernization under the gun of a regulatory deadline is exceptionally dangerous. Rushing complex architectural changes to appease an auditor frequently leads to catastrophic project collapse. To survive, engineering teams must deploy a highly pragmatic, phased architectural approach.
Avoiding the Big Bang: Why 70% of Transformations Fail
Attempting a massive, instantaneous cutover to a new cloud architecture while facing a hard compliance deadline is a recipe for disaster. The "big bang" modernization strategy carries a historically massive failure rate. McKinsey and Gartner note that up to 70% of large-scale digital transformations fail to deliver their intended impact, either running hopelessly over budget or failing completely [32].
When you rush a big bang release, you are forced to make architectural compromises. You lift-and-shift monolithic applications into Kubernetes without actually decoupling the internal dependencies. You end up with distributed monoliths that are harder to debug, more expensive to run, and still fail to provide the real-time telemetry regulators require. This phenomenon is known as compliance theatre. You check the box for the auditor, but you have actually increased your operational fragility.
To mitigate this 70% failure rate, successful CTOs adopt a phased Trojan Horse strategy. They decouple the immediate regulatory requirement from the long-term structural overhaul.
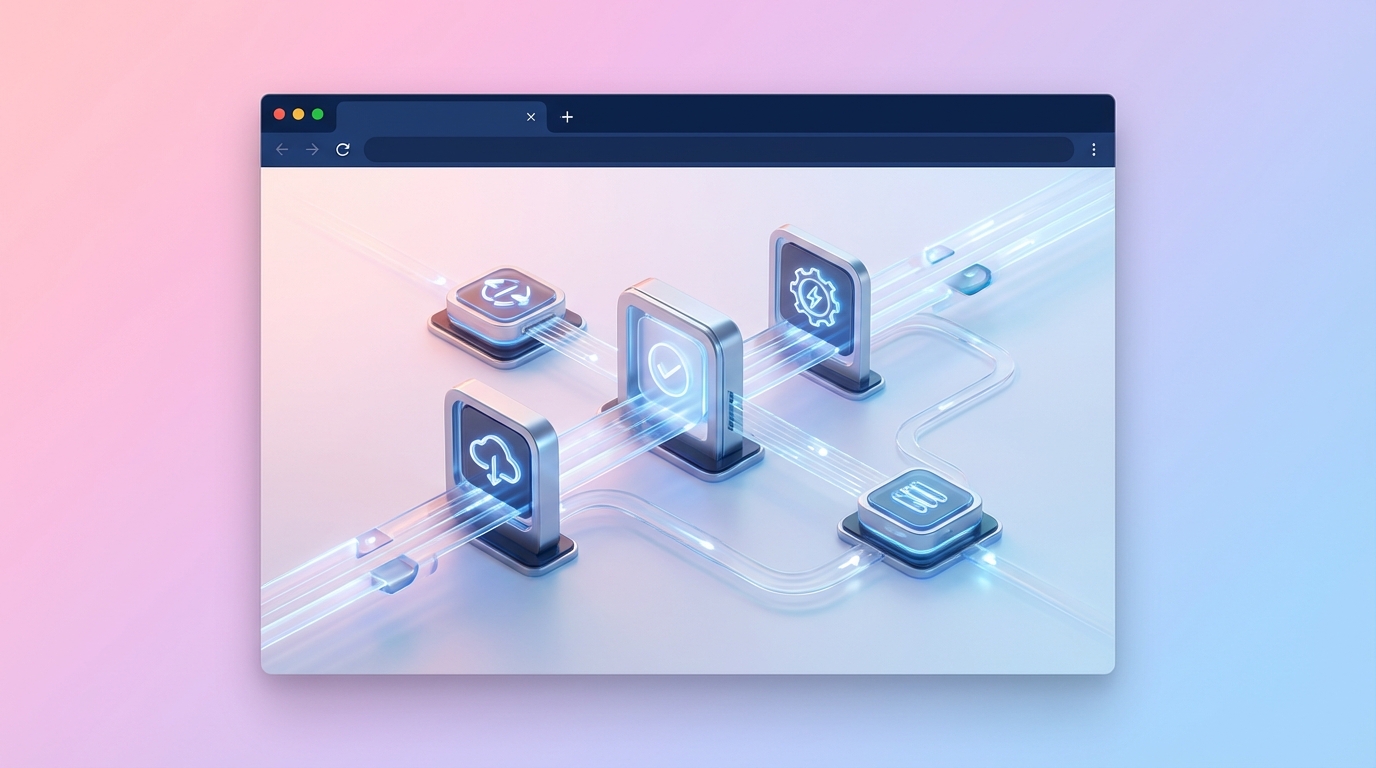
Phase 1: Tactical API Translation and Data Lakes
Phase 1 focuses exclusively on tactical compliance. The goal is to satisfy the auditor immediately while establishing a modern foothold in the infrastructure. You do not try to rewrite the core billing engine or the legacy ledger in six months. Instead, you wrap the legacy core.
Engineering teams deploy modern API translation layers, often utilizing API gateways and service meshes, to sit in front of the legacy monolith. These gateways handle the modern compliance requirements that the monolith cannot support. They enforce OAuth2, mutual TLS, and granular rate limiting. They act as a secure buffer, translating modern, compliant JSON REST requests into the SOAP or binary formats the legacy system expects.
Simultaneously, you establish a modern data layer or data lake. Instead of running heavy, slow compliance queries directly against the fragile legacy transactional database, you use Change Data Capture (CDC) tools to stream data out of the legacy system and into a modern event stream like Kafka. This data is then hydrated into a modern analytical datastore.
When the NIS2 auditor demands a real-time incident report, or the DORA mandate requires an immediate view of systemic risk, the query runs against the newly funded, high-performance data lake. The legacy system remains untouched and operational, isolated from the heavy read-loads of compliance reporting. You have successfully used the compliance budget to purchase and deploy a modern API gateway, an event streaming cluster, and a cloud data lake.
Phase 2: Strangling the Monolith
With Phase 1 complete, the business is legally compliant, and the immediate regulatory pressure is relieved. You now have a funded, operational modern infrastructure layer running in production. Phase 2 exploits this footprint to gradually dismantle the technical debt without needing to request a separate, hard-to-justify innovation budget.
This phase relies heavily on Martin Fowler's Strangler Fig pattern. Because all inbound traffic and outbound data reads are now routed through your modern API translation layer, you can safely begin decoupling specific domains from the monolith behind the scenes.
You select a specific bounded context, such as user notification preferences or basic profile management. You build that discrete service in the new cloud-native architecture. Once tested, you simply update the routing rules at the API gateway to point traffic for that domain to the new microservice instead of the legacy monolith.
The blast radius is inherently limited. If the new service fails, you revert the routing rule at the gateway, sending traffic back to the legacy core. Slowly, over the course of 18 to 24 months, more and more domains are strangled out of the monolith and rebuilt in the modern stack. Eventually, the monolith is hollowed out, handling almost no traffic, and can be safely decommissioned.
This phased approach guarantees that the enterprise remains legally operational during the heavy lifting. It ensures that the engineering team delivers continuous, incremental value while completely replacing the foundational infrastructure.
Looking Ahead: Compliance as a Continuous Pipeline Constraint
The regulatory landscape of 2025 to 2027 is a watershed moment for enterprise architecture. The organizations that merely bolt on manual workarounds to pass the next audit will find themselves crushed by operational overhead and eventual fines. The ultimate goal of this compliance-driven modernization is not just to survive the current batch of mandates, but to fundamentally alter how governance is enforced at the engineering level.
Shifting from Post-Hoc Checks to CI/CD Integration
Historically, compliance was a gatekeeper at the end of the software development lifecycle. Code was written, tested, and staged, and then a security or compliance team would spend three weeks running manual checks before approving the release. This model is dead. In a world where NIS2 demands 24-hour incident reporting, deployment velocity cannot be stalled by manual reviews.
The modernized architecture purchased via the Trojan Horse strategy allows teams to shift from post-hoc checks to continuous CI/CD integration. Compliance becomes codified. By utilizing tools like Open Policy Agent (OPA), engineering teams enforce compliance as code. If a developer attempts to commit an infrastructure-as-code template that provisions a storage bucket without the mandatory DORA-compliant encryption tags, the CI pipeline automatically fails the build. The policy is evaluated in milliseconds.
By enforcing these rules programmatically within the pipeline, you prevent the accumulation of future technical debt. Developers get immediate feedback, and auditors get cryptographically verifiable proof that every piece of infrastructure deployed in production meets the regulatory standard.
Automated Telemetry as the New Baseline
Real-time telemetry transitions from a luxury to an absolute baseline requirement. Modern architectures leverage technologies like eBPF (Extended Berkeley Packet Filter) to gain deep, kernel-level visibility into system performance and network traffic without modifying application code. Distributed tracing frameworks, such as OpenTelemetry, become mandatory to track requests across decoupled microservices.
This level of automation ensures that when an anomaly occurs, the system does not wait for a human analyst to notice a spike on a dashboard. Automated alerts trigger instant, isolated incident reports, satisfying stringent SLA mandates. The burden of discovery is shifted from human operators to autonomous systems, drastically reducing the Mean Time to Detect (MTTD) and ensuring compliance with the tight reporting windows dictated by European regulators.
The Long-Term Competitive Advantage
Organizations that successfully navigate this 2025-2027 regulatory cluster will possess highly resilient, real-time architectures. By leveraging compliance deadlines to fund the Strangler Fig pattern, these companies will systematically retire the 42% maintenance premium associated with legacy systems. The total cost of ownership drops significantly once the legacy mainframes are finally powered down.
More importantly, these organizations will outpace competitors who remain trapped in a cycle of reactive legacy patching. A modern, event-driven architecture built to satisfy PSD3 or the EU AI Act is inherently scalable. The same data lake funded to appease auditors can be utilized by data science teams to drive real-time customer analytics. The same API gateway deployed to handle eIDAS 2.0 authentication can be used to launch new mobile product offerings.
Compliance is the catalyst, but business agility is the true outcome. The regulatory pressure cooker is an opportunity to fix the foundation. CTOs who recognize this dynamic will fundamentally reshape their technology stacks, turning a legal mandate into a strategic competitive advantage.
For organizations facing the pressure of these 2025-2027 mandates, knowing where to start the Strangler Fig pattern is the hardest step. Altimi's Modernization Discovery Sprint delivers a concrete execution plan in 2 to 4 weeks. We provide a deep architecture assessment, a tactical 90-day roadmap for API translation and data decoupling, and a rigorous business case mapping CAPEX/OPEX projections to justify the investment. Start weaponizing your compliance deadlines for €8,500. Book a Modernization Assessment.
